Oxygen Forensics celebrates 24 years of innovation, excellence, and dedication to digital forensics.
Bringing insight and truth to data.
Oxygen Forensics is the leader in digital forensics and incident response. We provide digital forensic solutions to help make the world a safer place.
Contact Us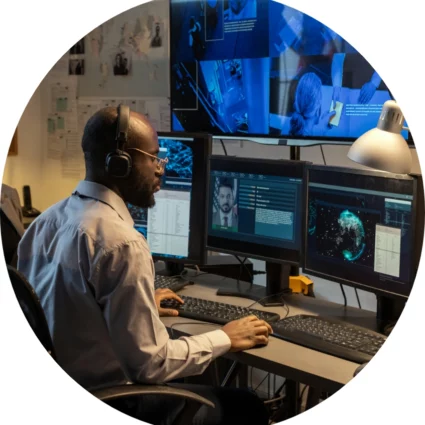

Who we help.
We provide digital forensic solutions to law enforcement, government agencies, organizations, and enterprises around the globe by bringing innovation to the investigative process and by empowering your workforce to resolve investigations and keep your organization safe.
Who We HelpLaw Enforcement & Government Agencies
Overwhelmed with the case backlog? Let us help. Upload multiple devices to a single platform, easily perform global searches with our AI-powered image categorization algorithms to quickly identify illicit materials, and work remotely and collaboratively.
Find out moreService Providers
Our best-in-class solutions assist service providers to maximize productivity and offer clients the information they need at a competitive price.
Find out moreEnterprise
Information technology has become part of every organization’s day to day. Extract data from multiple sources, monitor, analyze, and build reports all in one interface to align with privacy, compliance, and information governance.
Find out moreOur Products.
If you are looking for individual tools or a full digital forensic solution, we offer the most innovative tools you may need to simplify your workflow, gain insights from different sources, and strengthen your digital investigations to resolve cases faster and more efficiently.
Products
Oxygen Forensics Training Calendar - Check our classes and sign up today.
View Course Calendar